A crypto scam rarely ends with a clear answer. The money is gone, the platform disappears, and every transaction looks like a random string of letters and numbers. What actually happened in the background and where the funds went remain unclear.
This is where cryptocurrency scam investigations come in.
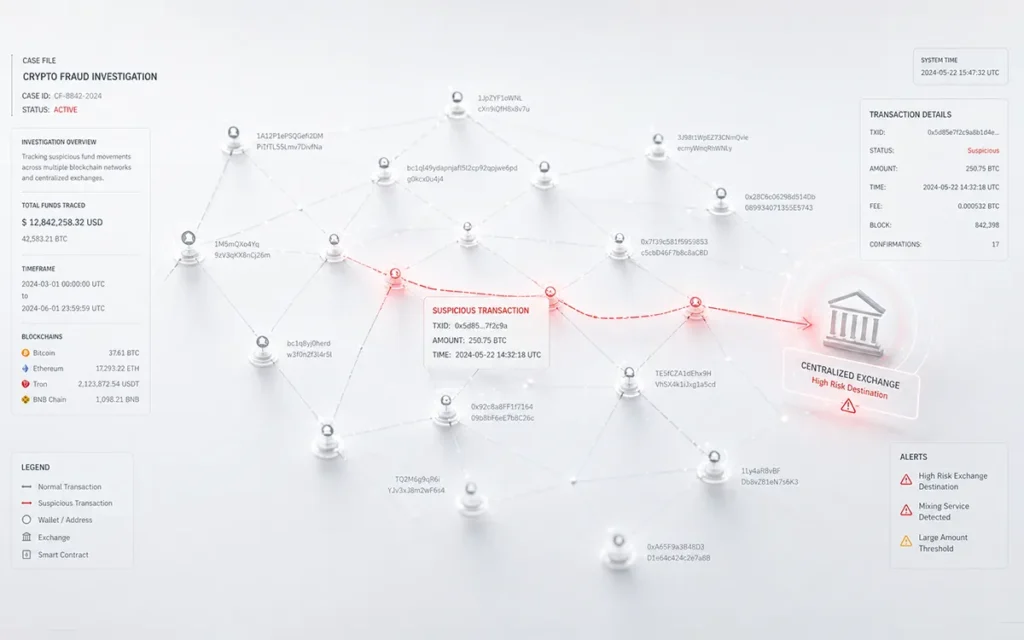
Behind every scam, there is a trail. Funds move from one wallet to another, get split, routed through multiple platforms, and sometimes converted across different tokens. From the outside, it feels impossible to follow. But investigators use blockchain data, tracking tools, and pattern analysis to piece that trail back together.
As crypto scams continue to grow globally, this process has become more important than ever. According to Chainalysis, billions of dollars are still lost to crypto scams each year, with fraud networks becoming more structured and harder to detect.
Understanding how these investigations work is no longer just technical knowledge. It is often the only way to make sense of a loss, and the first step toward any possible recovery.
Why Crypto Scams Are So Hard to Investigate
Cryptocurrency changed how money moves. No banks, no waiting time, no borders. Transactions happen fast, and control stays entirely with the holder.
That same design has also shaped how scams work.
Instead of forcing access, most scams are built to look real from the start. Fake investment platforms show steady profits that do not exist. Romance scams build trust over time and slowly introduce crypto transfers. Trading apps and bots promise automated gains but are designed only to collect deposits.
Common Types of Crypto Scams
1. Investment and Ponzi-style scams
Platforms promise high or guaranteed returns. Early withdrawals may work, creating trust, while new deposits are used to keep the system running. Learn more about how ponzi schemes work and how to identify them early.
2. Romance or long-term trust scams
Conversations build over weeks or months before any money is mentioned. By the time funds are sent, the connection feels real.
3. Fake trading platforms and bots
Dashboards, charts, and account balances appear active, but there is no real trading happening behind the scenes.
4. Phishing and wallet access scams
Fake apps, emails, or websites trick users into sharing private keys or seed phrases, giving full control of the wallet instantly. See how fake crypto investment platforms use phishing to steal wallet access.
How These Crypto Scams Actually Work
What makes these scams harder to deal with is what happens next.
The moment funds are sent, they are rarely left sitting in one wallet. Instead, they begin to move quickly and in patterns that are designed to confuse.
A single transfer can be broken into smaller amounts and sent across multiple wallet addresses. From there, funds may pass through different platforms, swapped into other tokens, or routed through services designed to hide transaction trails.
In some cases, this all happens within minutes.
By the time the loss becomes clear, the original transaction is only the starting point. What follows is a chain of movements, often spread across dozens of wallets and platforms.
This layering is not random. It is done to make tracking difficult.
Each step adds distance between the source of the funds and where they finally end up. Wallets do not carry names, transactions cannot be reversed, and platforms may operate across different regions.
This is exactly why cryptocurrency scam investigations are not simple.
The real challenge is not identifying the first transfer, it is following everything that comes after
How Does a Crypto Scam Investigation Work?
A cryptocurrency scam investigation is not a single step. It is a process that builds over time, using both technical tracking and legal coordination.
While every case is different, most investigations follow a similar path.

1. Evidence Collection
The process starts with what is available. This includes wallet addresses, transaction IDs, screenshots, emails, and any communication with the platform or individual involved. Even small details can make a difference later. A single wallet address or message can help connect a much larger trail.
2. Tracing the Movement of Funds
Once the details are gathered, the next step is to follow the money. Investigators use blockchain data to track how funds move from one wallet to another. This is not limited to one or two transfers. In most cases, funds are routed through multiple addresses, sometimes across different platforms or tokens.
3. Identifying Patterns
As the trail builds, patterns start to appear. Funds may be split into smaller amounts, moved rapidly between wallets, or passed through services designed to make tracking harder. These patterns are not random. They often point to how the scam was structured and how the funds are being handled.
4. Interaction With Platforms and Exchanges
If the funds reach a centralized platform, there may be a point of intervention. Investigators can work with exchange compliance teams by presenting verified transaction data. In some cases, this can lead to accounts being flagged or restricted while further action is taken.
5. Building a Case
All findings are then compiled into a structured report. This includes transaction trails, linked wallet activity, and any identifiable connections. The goal is to create a clear, evidence-backed view of what happened.
6. Coordinating Recovery Efforts
Recovery is not always guaranteed, but early action improves the chances. Once the trail reaches a point where identities or platforms are involved, the case can be taken forward through legal channels or enforcement agencies, depending on the situation.
Who Handles These Investigations?
By this stage, one thing becomes clear: these cases are not simple to handle alone.
Crypto scam investigations are usually carried out by a combination of specialists. Blockchain analysts track the movement of funds. Digital forensic experts organise and validate evidence. Legal teams step in when coordination with platforms or authorities is required.
Some firms bring all of this together under one process.
For example, Capx Recovery works on cases by combining transaction tracing with legal coordination. The process often starts with analysing the victim’s evidence and mapping how funds moved across wallets and platforms.
What makes these investigations possible is not access to hidden data, but the ability to understand what is already visible. Every transaction leaves a record. The challenge is connecting those records in a way that leads somewhere actionable.
Red Flags of a Crypto Scam

Most crypto scams follow similar patterns. Spotting these early can prevent the situation from turning into a full investigation later.
1. Unrealistic Returns
Promises of quick or guaranteed profits are a clear warning sign. No real investment can offer fixed returns without risk.
2. Pressure to Act Quickly
Scammers often create urgency, limited-time offers, “act now” messages, or claims that funds are at risk. This is meant to rush decisions.
3. Fake Endorsements or Hype
Claims of celebrity backing or trusted names are often used to build credibility. These are usually false and designed to gain trust quickly.
4. Requests for Secrecy
Being told to keep the investment “private” or not discuss it with others is a major red flag. Legitimate opportunities do not rely on secrecy.
5. Unusual Payment Requests
Requests to send funds to a new or unfamiliar wallet address without proper verification should raise concern. Once sent, transactions cannot be reversed.
6. Unverified Platforms or Apps
Websites or apps with no clear ownership, history, or licensing are often part of scam setups. They may look real but disappear once enough deposits are collected.
Recognising these signs early can stop a scam before it begins. And if something still goes wrong, understanding these patterns also helps explain how the scam unfolded during an investigation.
Can Crypto Scam Losses Be Recovered?
By now, the process is clearer. Funds can be traced, patterns can be identified, and action can be taken in some cases.
The next question is the one most people are trying to answer from the start:
Can any of it be recovered?
There is a common belief that once crypto is lost, it is gone for good. That is not always true. Crypto investment scam recovery is difficult, but it is possible in certain situations, especially when action is taken early. Investigations can track how stolen funds move across wallets and identify points where they interact with platforms. If those funds reach a centralized exchange or a service that follows compliance rules, there may be an opportunity to intervene.
This is where timing matters.
The longer the delay, the greater the distance is created between the original transaction and where the funds end up. As the trail becomes more layered, recovery becomes harder.
There are also a few things that make tracking stolen crypto harder:
1. Mixing services
These tools mix stolen money with other transactions, so it becomes difficult to tell which funds belong to whom.Our guide on cryptocurrency forensics explains how investigators track funds even through mixing services.
2. Fast movement between wallets
The money is quickly split and sent to many different wallet addresses to confuse the trail.
3. Moving across different blockchains
Funds can be shifted from one network to another, which makes tracking more complicated.
4. Privacy-focused coins
Some cryptocurrencies are built to hide transaction details, making them much harder to trace.
Because of all this, every case is different, and results can vary.
What improves the chances is early reporting, accurate evidence, and a clear understanding of how the funds moved. Even when full recovery is not possible, investigations can still uncover where the money went and how the scam was carried out.
How to Report a Crypto Scam (And What to Do Next)
Once a scam is identified, the next steps matter more than anything else. Quick action does not guarantee recovery, but delays almost always make things harder.
The following is a step-by-step method that you should consider in case of a cyber scam:
1. Collect and Organize Your Evidence
To start with, collect any document that has anything to do with the process of the transaction.
Wallet address, transaction ID, screenshot of your interaction, emails, chat history, and the link to the platform itself are all essential. Even small details can help build a clearer picture of how the scam unfolded.
2. Report to the Relevant Authorities
Filing a report creates an official record of the incident.
Report to Law Enforcement
- FBI Internet Crime Complaint Center (IC3)—Best for US victims of crypto fraud.
- Federal Trade Commission (FTC)—For scams involving deceptive business practices.
- Securities and Exchange Commission (SEC)—If it involves an investment scheme.
Depending on the location, this may involve cybercrime units, financial regulators, or consumer protection bodies. These reports can support further action, especially if the case connects to a larger fraud network.
3. Inform the Platform or Exchange
If the funds were sent to or passed through a centralized platform, report it to their support or compliance team.
Providing verified transaction details early can sometimes help flag suspicious activity or restrict further movement, depending on the situation.
4. Flag the Wallet Address
Scam-related wallet addresses can be reported on public blockchain explorers and fraud databases.
This does not reverse the transaction, but it helps build visibility and may prevent others from falling into the same trap.
5. Consider Professional Investigation Support
In more complex cases, tracing the movement of funds may require deeper analysis.
This is where investigation-focused firms can step in. For example, Capx Recovery works on tracing transaction flows and supporting cases where technical tracking and legal coordination are both required.
Taking these steps early helps preserve the trail while it is still easier to follow. Even when outcomes vary, timely reporting and structured action can make a meaningful difference in how a case progresses.
Protecting Your Digital Wealth
Cryptocurrency scams do not stop once the money is transferred. This is where things begin for real. While it seems like money vanished into thin air, there is a possibility that the transfer left a trail that can be traced and analyzed via a cryptocurrency scam investigation.
A crypto fraud investigation aims to make sense of a seemingly hopeless situation. The process will enable you to trace where the money went, understand how the scheme works, and find out what can still be done.
But timing is everything in such cases.
For those dealing with a situation like this, speaking with teams that handle cryptocurrency scam investigations, such as Capx Recovery, can help make sense of what happened and what steps can be taken next. Contact them today to get the guidance you need.
FAQs
Who Are Crypto Scam Investigators?
They’re specialists in blockchain forensics, OSINT, and legal compliance. Using advanced analytics tools, they follow transactions linked to scam-detected Bitcoin addresses and connect them to real-world identities.
Can You Be Scammed by Sending Someone Cryptocurrency?
Yes. Once you send crypto, the transaction is irreversible. If the recipient is a scammer, they can instantly move or launder your funds. Always verify the recipient before sending.
What Evidence Do I Need to Recover Stolen Crypto?
Wallet addresses, transaction IDs, screenshots of communications, platform URLs, and any payment confirmations. The more data you provide, the higher the chance that investigators can trace and freeze funds.