Mainstream adoption of cryptocurrency has occurred together with an increase in cryptocurrency-related scams. Your funds become accessible through every type of wallet, which includes both mobile wallets and hardware wallets. Attackers choose to target this method because it has no banking system that can reverse unauthorized payments.
The numbers tell the story. In 2025, global crypto scam losses were estimated to exceed $5 billion, with phishing attacks, fake investment platforms, and social engineering leading the surge. Most victims who experienced the incident were not careless because they lacked the ability to prevent the situation from occurring.
Most attacks don’t rely on hacking complex systems. They rely on tricking people. A fraudulent website presents itself as a legitimate site. A message that feels urgent. A “support agent” who requests your seed phrase information.
The guide presents practical information through its explanations. The reader will learn to protect their crypto wallet through stepwise instructions, which show them how to identify warning signs and respond properly to any problems that occur.
Why Crypto Wallet Security Matters More Than Ever
A crypto wallet isn’t just an app or a device. It’s full control over your assets. That control comes with a tradeoff. If something goes wrong, there’s usually no safety net.
Unlike traditional banking, crypto transactions are irreversible. Once funds leave your wallet, they’re gone unless you can track and recover them quickly. That’s why attackers don’t try to break the blockchain. They target you.
Over the past year, scams have become more targeted and more convincing. Many users who lost funds didn’t ignore security. They were misled at the right moment.
Here’s why wallet security is critical right now:
- No centralized protection
There’s no bank or authority to reverse fraudulent transactions
- Rising phishing attacks
Fake websites, emails, and apps are getting harder to detect
- Seed phrase vulnerability
Anyone with your recovery phrase can access your funds instantly
- Growth of DeFi risks
Smart contracts and dApps introduce new attack surfaces
- Human error is the biggest weakness
Most scams succeed through manipulation, not technical hacks
Crypto gives you full ownership. But it also makes you fully responsible.
Understanding the risks is the first step. The next is knowing exactly how to protect yourself.
Most Common Crypto Wallet Scams in 2026
Crypto scams have evolved. They’re no longer obvious or poorly written. Many look professional, feel urgent, and mimic real platforms almost perfectly.
Most attacks fall into a few repeatable patterns. Once you recognize them, it becomes much easier to avoid getting caught.
| Scam Type | How It Works | Warning Signs |
| Phishing Websites | Fake sites copy real wallet or exchange login pages to steal credentials | Slight URL changes, fake emails, urgent login requests |
| Fake Wallet Apps | Malicious apps mimic trusted wallets and steal private keys | Found outside official stores, with low reviews, and strange permissions |
| Seed Phrase Scams | Scammers ask you to “verify” or “recover” your wallet using your phrase | Any request for a seed phrase is a scam, no exceptions |
| Investment Scams | Fake platforms promise guaranteed returns or “AI trading profits” | Unrealistic gains, pressure to deposit quickly |
| Romance/Trust Scams | Scammers build relationships, then ask for crypto transfers | Emotional manipulation, sudden financial requests |
A key trend in 2025 carried into 2026: over 60% of crypto scams involve phishing or impersonation tactics. That means most attacks don’t break systems; they trick users into giving access.
Another shift is how scams are delivered. Instead of random spam, attackers now use:
- Social media DMs
- Fake customer support accounts
- Telegram and Discord communities
- Search ads leading to fake websites
If you’re using DeFi wallets or interacting with dApps, the risk increases even more due to smart contract permissions and token approvals. For a deeper breakdown of DeFi-specific risks, you can read this guide.
The takeaway is simple. Scams are getting smarter, but they still rely on predictable tactics. Once you know what to look for, most of them become easy to spot.
How to Protect Your Crypto Wallet (Step-by-Step)
Protecting your wallet isn’t about one setting or one tool. It’s a combination of habits. When done right, it makes you a very hard target.
Step 1: Choose a Secure Wallet
Start with the foundation. Not all wallets are built the same.
- Prefer well-known, audited wallets
- Use hardware wallets for long-term storage
- Only download from official websites or app stores
- Avoid links shared through ads or DMs
A secure wallet reduces risk, but only if you set it up correctly.
Step 2: Use Strong Passwords + 2FA
Weak passwords are still one of the easiest ways attackers get in. Create a strong password to secure your account using the tips below.
- Use a unique password for each wallet or exchange
- Avoid reusing passwords across platforms
- Enable 2FA using an authenticator app, not SMS
- Consider a password manager for secure storage
Step 3: Protect Your Seed Phrase
This is the most important rule in crypto.
- Write your seed phrase on paper or a metal backup
- Store it in a safe, offline location
- Never take screenshots or store them in cloud storage
- Never share it with anyone, even “support teams”
If someone has your seed phrase, they have your wallet. No exceptions.
Step 4: Verify Every Transaction
Small mistakes can lead to permanent loss.
- Double-check wallet addresses before sending
- Use a small test transaction before large transfers
- Watch out for malware that changes copied addresses
- Confirm network fees and destination chain
Step 5: Stay Alert to Phishing Attempts
Most scams start with a link.
- Bookmark official wallet and exchange websites
- Don’t click links from emails, ads, or random messages
- Always check domain names carefully
- Ignore urgent messages asking for action
Step 6: Use Cold Storage for Large Funds
Think of this as your savings vault.
- Keep the majority of funds in offline (cold) wallets
- Use hot wallets only for daily transactions
- Disconnect wallets from dApps when not in use
Strong security isn’t complicated. It’s consistent. If you follow these steps, you eliminate the majority of real-world crypto threats before they even reach you.
Red Flags That Signal a Crypto Scam
Most scams follow the same psychological playbook. They create urgency, build trust quickly, and push you to act before you think.

If something feels slightly off, it usually is.
Watch for these common warning signs:
- Guaranteed profits or “risk-free” returns
No legitimate crypto investment can promise consistent gains
- Urgent messages pushing quick action
Phrases like “act now,” “limited time,” or “account at risk” are designed to pressure you
- Requests for private keys or seed phrases
No real platform, wallet, or support team will ever ask for this
- Unknown platforms asking for deposits first
Especially if withdrawals are “locked” until you add more funds
- Impersonation of trusted brands or influencers
Fake support accounts, cloned websites, or deepfake videos
- Too-good-to-be-true opportunities
High returns with little explanation usually mean high risk or outright fraud
- Unverified links in emails, ads, or DMs
Many scams start with a single click
The pattern is simple. If there’s pressure, secrecy, or unrealistic rewards, step back. Catching these signals early is often the difference between staying safe and losing funds.
What to Do If Your Crypto Wallet Is Compromised
If your wallet is compromised, speed matters. The faster you act, the better your chances of limiting damage.
Don’t panic. Focus on containment first, then recovery.
Immediate Actions
- Transfer remaining funds immediately
Move assets to a new, secure wallet you control
- Disconnect from all dApps
Revoke wallet access from any connected platforms
- Revoke token approvals
Use tools like Etherscan or Revoke.cash to remove permissions
Secure Your Accounts
- Change passwords for wallet apps, exchanges, and email
- Enable or reset 2FA using an authenticator app
- Scan your device for malware or suspicious extensions
- Remove unknown apps or browser plugins
Document Everything
You’ll need this for reporting and possible recovery.
- Transaction IDs (TXIDs)
- Wallet addresses involved
- Screenshots of messages, websites, or apps
- Timeline of what happened
Isolate the Cause
Try to identify how the breach happened:
- Clicked a phishing link?
- Installed a fake wallet or extension?
- Shared your seed phrase unknowingly?
This helps prevent repeat attacks. Check a deeper recovery checklist.
The goal isn’t just to react. It’s to stop further loss, secure what’s left, and prepare for the next step, which is reporting and tracking the scam.
How to Report Crypto Scams (Step-by-Step)

Reporting a scam won’t always reverse the transaction, but it does two important things. It increases your chances of recovery and helps authorities track larger fraud networks.
Act quickly and report across multiple channels.
Step 1: Report to Government Authorities
Start with official reporting platforms. This creates a formal record of the incident.
- FTC (Federal Trade Commission)
Report fraud at reportfraud.ftc.gov
- IC3 (FBI Internet Crime Complaint Center)
Best for larger losses or organized scams
Provide clear details, including wallet addresses, transaction IDs, and how the scam happened.
Step 2: Report to Crypto Platforms
If the transaction involved an exchange or wallet provider:
- Contact their support team immediately
- Share transaction details and scam evidence
- Request account monitoring or temporary holds if possible
Some platforms can flag suspicious addresses or assist with tracing.
Step 3: Report Scam Websites and Links
Help prevent others from falling into the same trap.
- Report phishing sites to Google Safe Browsing
- Flag domains through hosting providers or registrars
- Report fake apps to app stores
This can lead to faster takedowns.
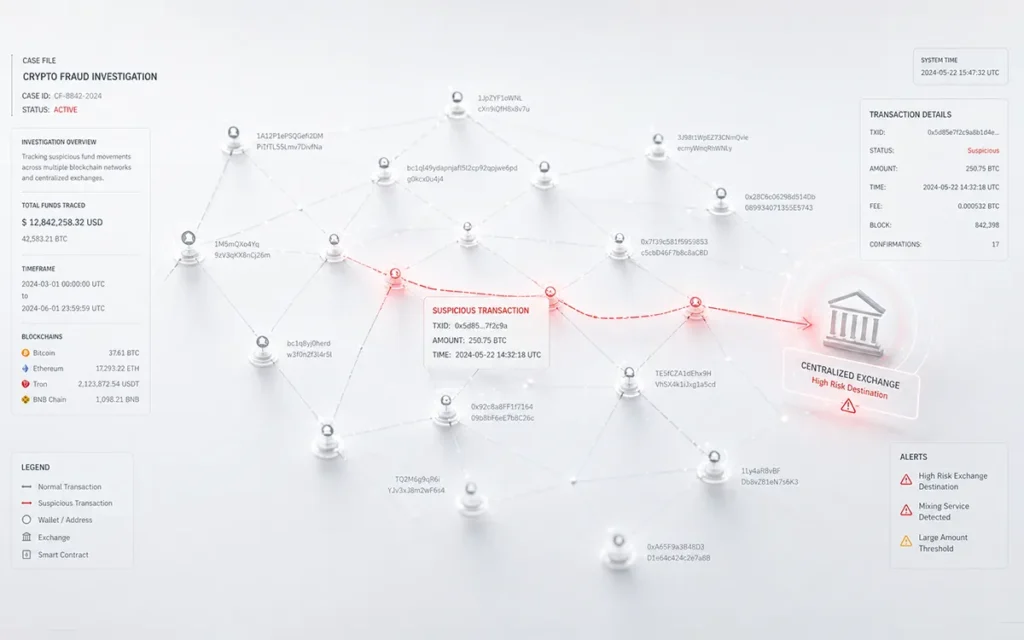
Step 4: Track the Transaction
Even though crypto is decentralized, it’s also transparent.
- Use blockchain explorers (like Etherscan or Blockchain.com)
- Track where funds are moving
- Identify linked wallets if possible
Sharing this data with authorities or recovery experts can help build a case.
Step 5: Warn Others
This step is often overlooked but powerful.
- Share scam details on forums like Reddit or Twitter.
- Post wallet addresses involved in the scam
- Alert community groups (Telegram, Discord)
Scammers rely on silence. Visibility works against them. Get professional help with tracking or recovery.
Reporting may feel like a long shot, but it’s a critical step. Many large scam networks have been uncovered because multiple victims reported early and shared details.
Can You Recover Stolen Crypto?
This is the question most people ask first, and the honest answer is this. Recovery is possible, but it depends heavily on timing and the path your funds take.
Crypto transactions can’t be reversed, but they can be traced. Every movement is recorded on the blockchain. That creates an opportunity, especially if the funds haven’t been fully laundered or moved through multiple layers.
Here’s what affects recovery chances:
- How quickly you act
Faster reporting increases the chances of tracking funds
- Where the funds were sent
Transfers to exchanges are easier to flag than private wallets
- Complexity of the scam
Advanced scams often move funds across chains or use mixers
- Quality of evidence
Clear transaction data and documentation help build a case
In some cases, exchanges can freeze assets if they receive timely reports. In others, blockchain analysis can identify patterns and wallet clusters linked to scam networks.
The key is simple. Don’t wait. The sooner you respond, the better your chances of limiting loss and possibly recovering what’s gone.
Quick Crypto Security Checklist
If you want a simple way to stay protected, this is it. Run through this checklist regularly and fix any gaps.
| Action | Status |
| Use a hardware wallet for long-term storage | ✓ |
| Enable 2FA (authenticator app, not SMS) | ✓ |
| Store seed phrase offline (paper or metal) | ✓ |
| Never share private keys or recovery phrase | ✓ |
| Bookmark official wallet and exchange sites | ✓ |
| Double-check wallet addresses before sending | ✓ |
| Avoid clicking links from emails or DMs | ✓ |
| Revoke unused dApp permissions regularly | ✓ |
| Keep wallet apps and devices updated | ✓ |
| Use separate wallets for trading and storage | ✓ |
This isn’t complicated, but it’s effective.
Most real-world crypto losses happen because one of these steps was skipped. Keeping these basics covered puts you ahead of the majority of users and far out of reach for most common scams.
Future Trends: How Crypto Scams Are Evolving (2026 Insights)
Scams aren’t slowing down. They’re getting sharper, more personalized, and harder to detect.
One of the biggest shifts is the use of AI-generated content. Phishing emails now sound natural. Fake websites look identical to real ones. Even voice and video deepfakes are being used to impersonate influencers or support teams.
At the same time, attackers are moving deeper into the ecosystem:
- DeFi exploits are increasing as more users connect wallets to dApps
- Social engineering is becoming more targeted, using personal data from social media
- Fake job offers and collaboration requests are being used to trick users into installing malware
- Cross-chain scams are making fund tracking more complex
Another trend is patience. Scammers are no longer rushing. They build trust over days or weeks before making a move.
Industry reports suggest that AI-driven scams could see significant growth through 2026, especially in phishing and impersonation attacks.
The takeaway is simple. Security isn’t a one-time setup anymore. It’s something you actively maintain as the threat evolves.
Stay Safe, Stay in Control
Crypto gives you full ownership of your money. That’s powerful, but it also means you’re the first and last line of defense.
The good news is this. Most scams aren’t unstoppable. They rely on small mistakes, rushed decisions, or a lack of awareness. Once you understand how they work, they become much easier to avoid.
If you take away anything from this guide, let it be these three things:
- Never share your seed phrase
- Always verify before you click or send
- Act fast if something feels wrong
Security isn’t about doing everything perfectly. It’s about being consistent with the basics.
And if you ever find yourself dealing with a scam, don’t ignore it or wait it out. Take action, report it, and explore recovery options early.
FAQ
What should I do immediately after a crypto scam?
Move your funds to a safe wallet, revoke wallet permissions, change passwords, enable 2FA, and report the scam to authorities like the FTC or FBI IC3. Quick action improves recovery chances.
Can stolen cryptocurrency be recovered?
Stolen crypto can sometimes be recovered if reported quickly and tracked on the blockchain. Recovery depends on where the funds were sent and how fast action is taken.
What is the safest way to store cryptocurrency in 2026?
The safest way to store crypto is by using a hardware wallet with your seed phrase stored offline. Avoid keeping large amounts in hot wallets or exchanges.
How do I protect my crypto wallet from scams?
Use strong passwords, enable 2FA, never share your seed phrase, verify all links, and avoid unknown apps or platforms. Most scams can be prevented with basic security habits.